Technology-facilitated abuse is a real issue in Australia, and forensic cyber experts say it’s important to know how your devices can be compromised.
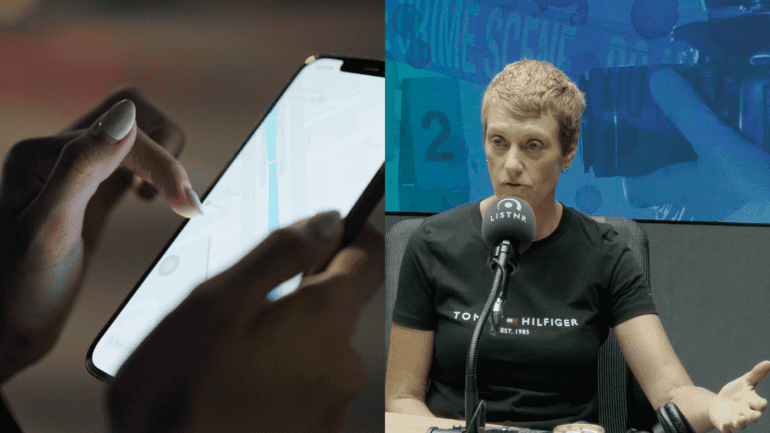
“A mobile phone can be compromised in a variety of ways,” says Rose MacDonald, CEO of Nansen Digital Forensic Services.
“That can be as simple as downloading a specific application that is designed to spy.”
MacDonald works with domestic violence agencies to identify how victim survivors might be targeted through their devices.
MacDonald told Crime Insiders how spyware can infiltrate your devices:
“Many people use functions like family sharing,” she said, “a really common way to keep in touch. Know where people are, know that they’re safe,”
“But it can also be used in a nefarious way, and we see a lot of that.”
MacDonald profiles victim-survivors in terms of their social media, their devices and home environment.
“Even if a perpetrator doesn’t have access to a physical device, if they breach the cloud environment,” she said.
Most mobile devices are linked to a cloud account, for example, if a Gmail account is linked to a Google account, this can be infiltrated.
“Then they access every application that sits in that environment. Being your emails, your maps, location data, a whole range of stuff that sits in that environment.”
Hear about the different ways your devices can be used to spy on this episode of Crime Insiders.
If you or someone you know is impacted by technology-facilitated abuse, you can call 1800RESPECT or visit safesteps.org.au
Subscribe to Crime Insiders, taking you beyond true crime. In groundbreaking interviews, explore the world of policing and forensics through stories from the world’s most experienced and decorated experts.